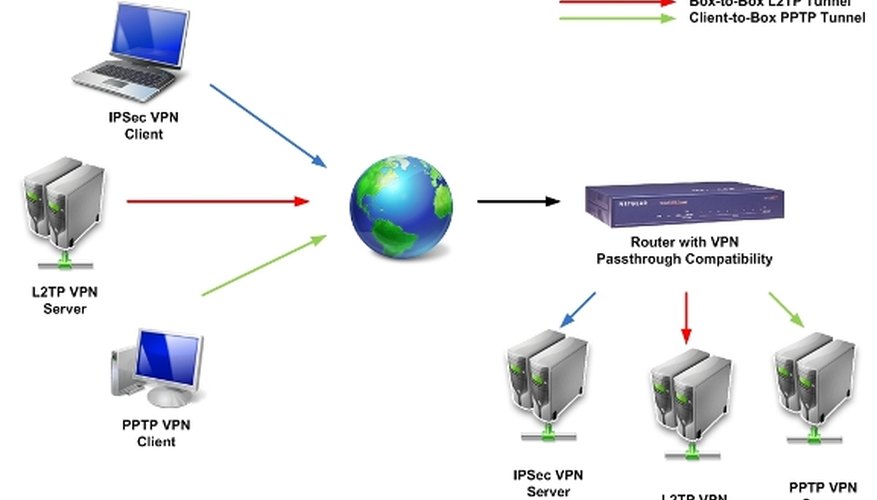
VPN Passthrough is a setting on routers to allow a secure virtual private network (VPN) connection between two computers. Setting the router's VPN Passthrough setting will open a VPN port and enable the connection to pass through the router without interruption. Not all routers support the VPN Passthrough configuration. Consult the manufacturer's website or router product manual to verify the hardware configuration.
Open an Internet browser on one of the computers on the local area network.
Type the router administration application's IP address into the URL input bar. Router administrative applications typically will have the IP address of 192.168.0.1 or 192.168.1.1. Consult the product manual for the correct IP address.
- VPN Passthrough is a setting on routers to allow a secure virtual private network (VPN) connection between two computers.
- Type the router administration application's IP address into the URL input bar.
Enter the administrative user ID and password, when prompted, to access the administrative interface.
Click the "Security" tab or link to access the router's security configuration.
Click "Enable PPTP Passthrough" option to turn on the passthrough function. Click "OK" and return to the main screen of the administrative application.
Click "Port Forwarding" option from the router administrative program's main screen.
- Enter the administrative user ID and password, when prompted, to access the administrative interface.
- Click "Port Forwarding" option from the router administrative program's main screen.
Enable port forwarding for PPTP on port number 1723. The process for enabling port forwarding will vary with different routers. For Netgear routers, select PPTP from the drop-down menu and add the port number into the port number input box.
To test the VPN connection between the two secure VPN-enabled computers, first, log on to one computer of the two VPN-enabled computers.
Click the Windows "Start" butten, then select "Network" from the "Programs" menu.
Click the "Network and Sharing Center" button on the top navigation bar of the Network window.
Locate the VPN connection icon and information in the Network and Sharing Center.
Double-click the VPN connection icon to connect to the second computer. If prompt is presented requesting user id and password, the VPN connection is successful.